What is Broken Access Control & Why Should You Care? 🤔
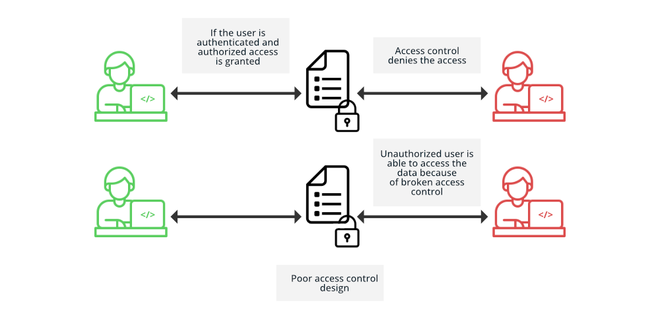
Imagine you’re in a hotel. You have a key card that should only open your room, but somehow, it unlocks every door in the building. That’s what Broken Access Control is in the digital world—it allows unauthorized users to access restricted data or perform actions they shouldn’t be able to.
According to the OWASP Top 10, Broken Access Control has been the #1 web security risk since 2021, causing massive breaches in companies worldwide. If ignored, it could lead to full system compromise, data leaks, or even complete account takeovers. 🚨
Real-World Security Breaches Due to Broken Access Control 🔥
This vulnerability isn’t just theoretical—it’s been the root cause of major cybersecurity disasters:
🛑 Facebook’s Data Leak (2019)
- What happened? A Broken Access Control flaw allowed attackers to scrape over 540 million Facebook records from exposed databases.
- Impact: Personal data of users, including phone numbers and comments, was exposed.
- Source: TechCrunch Report
🛑 Uber’s Admin Panel Hack (2016)
- What happened? Hackers bypassed authentication controls and accessed Uber’s admin dashboard, leaking personal info of 57 million users.
- Impact: A $148 million fine due to data privacy violations.
- Source: FTC Case Against Uber
These are just a few examples—many more companies fall victim every year due to weak access control mechanisms.
Common Broken Access Control Attacks & Exploits 🕵️♂️
Attackers use several techniques to manipulate access control flaws. Here are the most common ones:
1️⃣ Insecure Direct Object References (IDOR) – The Sneaky Backdoor 🚪
- Attackers modify URLs or request parameters to access unauthorized data.
- Example: A shopping site uses
/order?id=1234. A hacker changes it to/order?id=5678and views someone else’s order details.
2️⃣ Privilege Escalation – Gaining Unauthorized Power 🔺
- Attackers trick the system into upgrading their user privileges.
- Example: A regular employee finds a hidden admin panel (
/admin) and gains control over the system.
3️⃣ Session Hijacking & Forced Browsing – Jumping the Fence 🏃♂️
- Attackers guess, brute-force, or reuse expired sessions to bypass authentication.
- Example: An employee logs into a sensitive dashboard, but attackers reuse their session cookie to gain access.
4️⃣ Metadata & API Manipulation – Twisting the System 🤖
- Attackers alter JWT tokens, cookies, or API requests to change permissions.
- Example: A user modifies a JWT token to give themselves
admin=true, bypassing authorization checks.
4 Proven Ways to Prevent Broken Access Control ✅
The best way to fight hackers is to be proactive. Follow these best security practices to safeguard your applications:
🔐 1. Implement Role-Based Access Control (RBAC) & Least Privilege
- Ensure users only have access to what they need—nothing more.
- Use multi-layer authentication to prevent privilege escalation.
🛡️ 2. Enforce Strong Authentication & Secure Session Management
- Enable Multi-Factor Authentication (MFA) to block unauthorized logins.
- Expire inactive sessions and prevent session fixation attacks.
🛠️ 3. Use Security Testing & Automated Scanning
- Regularly scan applications using tools like:
- Conduct penetration testing to identify weak access points.
🚧 4. Validate & Restrict User Input Properly
- Implement server-side validation to block unauthorized requests.
- Use secure frameworks that enforce access control by default.
Final Thoughts: Protect Your Apps Before It’s Too Late! ⏳
Broken Access Control is a silent killer that continues to expose businesses to data breaches, hacking attempts, and compliance violations. If left unchecked, it could cost millions in fines and reputational damage.
By implementing strong access control mechanisms, regularly testing for security flaws, and restricting user permissions, you can protect your applications from unauthorized access and cyberattacks.
📢 Stay ahead of hackers! Subscribe to our blog for the latest cybersecurity insights and updates. 🔥
Wanna read more about OWASP top 10!!!



